top of page

AI Cyber Incident Tabletop Exercise Platform
Train your team and eliminate guesswork using AI cyber crisis simulations
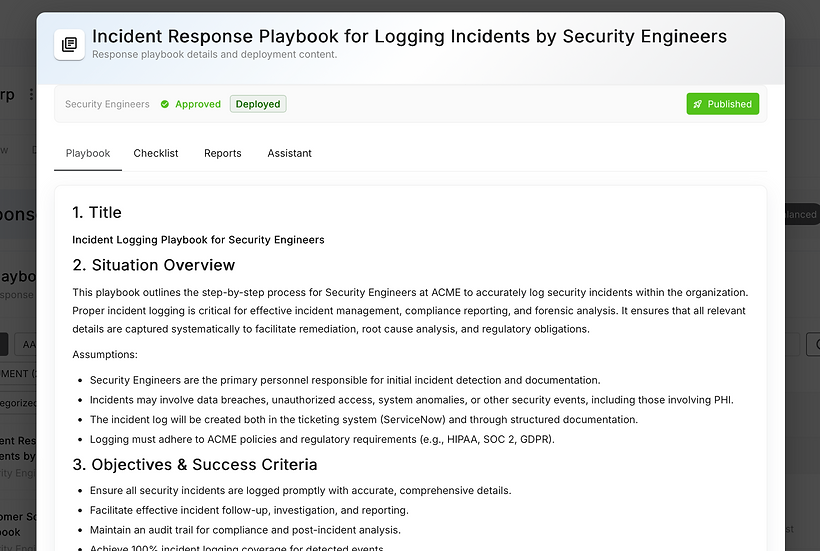
Orchestrate incident response across all business units in one place

Powered by OpsBook
Practice
Run AI cyber crisis simulations using 1,000s of custom scenarios and eliminate guesswork during a real breach
Evaluate
Review the results of your exercises using the platform-generated After-Action Review reports
Improve
Organize, orchestrate, and collaborate on all things breach response in one integrated, secure cloud platform
bottom of page